Hello,
I’m trying to set flow rules to allow only communication to destination PC10, and drop anything else.
PC20 must not communicate with PC30, and inversely.
To check if basis network is correct, I setup these rules :
# Allow IPv4, IPv4 ARP, and IPv6 frames.
drop
not ethertype ipv4
and not ethertype arp
and not ethertype ipv6
;
accept;
For testing, all firewalls on PC10, PC20, PC30 are disabled.
PC10, PC20, PC30 are authenticated in ZeroTier Central networks and have a manual IP (auto-assigned disabled)
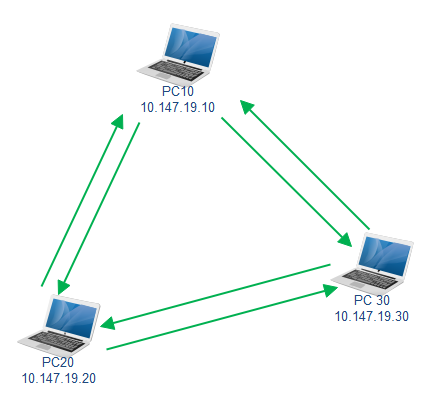
On PC10, I ping PC20 and PC30 : Reply OK
On PC20, I ping PC10 and PC30 : Reply OK
On PC30, I ping PC10 and PC20 : Reply OK
Well, everybody’s able to ping each other.
Now, I restrict communication modifying the flow rules :
# Allow only server communication, blocking everything except communications from and to PC10.
drop
not ipdest 10.147.19.10/24
or not ipsrc 10.147.19.10/24
;
# Allow IPv4, IPv4 ARP, and IPv6 frames.
drop
not ethertype ipv4
and not ethertype arp
and not ethertype ipv6
;
#accept;
After few seconds, rules are updated but behavior is illogical and not what I expected : only ping from PC10 to PC30 replies.
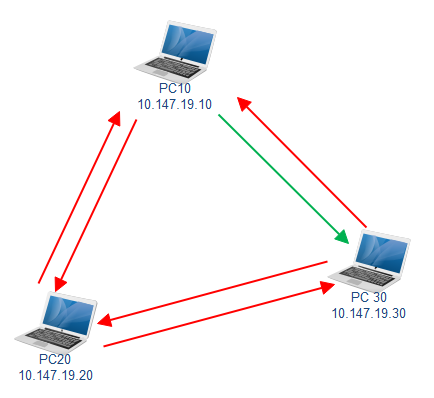
What did I missed ?
Thanks for your support !
Updating tests :
→ Switching the drop blocks one before the other doesn’t change anything.
→ Final accept; or #accept; leads to the same issue.
![]() Solution : not use ipdest/ipsrc
Solution : not use ipdest/ipsrc
→ The following flow rule works using ztdest and ztsrc !! :
drop not ethertype ipv4 and not ethertype arp;
drop not chr ipauth;
accept ztsrc xxxxxxxxxx or ztdest xxxxxxxxxx;
drop;